Tech
Denis Pakhaliuk on Designing, Developing, and Maintaining Secure Products

When developing new software, your software development life cycle’s success heavily relies on implementing security measures. For starters, it is essential to engage with stakeholders throughout the development process continually. Denis Pakhaliuk, Ramotion CEO, says that understanding and managing the stakeholder’s expectations guarantees that the final product’s success in the stakeholder’s eyes is in harmony with the design’s criticality. Engaging with them will help you avoid any potential surprises at the end. Similarly, enforcing traceability for requirements is another element that should be considered throughout the Software development life cycle. This serves to ease customer acceptance of the final product as it provides confidence that all requirements are met and tested.
Denis Pakhaliuk provides ways to infuse security into your software development life cycle.
Requirements Gathering Stage
According to Denis Pakhaliuk, the first step in this stage is to assess the landscape. You can get a strong understanding of what the customer wants by establishing the scope and boundaries, identifying stakeholders, identifying process gaps, and then scaling security-centric processes specifically tailored to the organization and the content of the project.
The next step is to consolidate an industry-standard security model. Integrating a trusted maturity model at the onset of your software development cycle secures the software you are building from the beginning and minimizes any costs that could negatively affect your budget.
All personnel involved in the project should then be educated on software security. To avoid insecure design and development practices, everyone involved in the project should be knowledgeable and up-to-date with software security standards.
To warrant that software security is integrated into the process, you need to assign responsibility formally.
The final step in this stage is to identify significant risks and institute a comprehensive risk management plan. Denis says that this ensures proper security design and allows you to stay within your schedule, goals, and budget.
Design Stage
In this phase, Denis Pakhaliuk emphasizes that it is vital that you perform architecture reviews to identify any flaws in your design and eliminate any threats to your model before you deploy the software. Aside from removing threats, this risk analysis can help you identify other flaws by analyzing essential design principles, assessing the attack surface, enumerating the different threat agents, and highlighting any security controls’ weaknesses.
Implementation Stage
In this stage, performing a secure code review reduces the number of bugs that could find their way into the finished product.
Verification Stage
During the verification phase, executing test plans will verify whether the product will perform as expected in runtime scenarios.
Deployment/Maintenance Stage
Denis says a deployment plan is vital for a successful release once acceptance testing is done. The project should encompass the environment of operation of the software and exact steps for configuring and launching. It should also involve plans for maintenance of the software and a process for change management that can handle any production bugs or requests for enhancement.
-
 Sports4 weeks ago
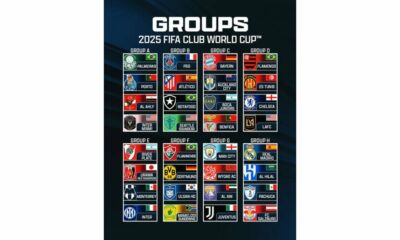
Sports4 weeks agoFIFA Club World Cup 2025: Complete List of Qualified Teams and Groups
-

 Sports3 weeks ago
Sports3 weeks agoAl Ahly vs Inter Miami, 2025 FIFA Club World Cup – Preview, Prediction, Predicted Lineups and How to Watch
-
Health2 weeks ago
Back to Roots: Ayurveda Offers Natural Cure for Common Hair Woes
-

 Tech2 weeks ago
Tech2 weeks agoFrom Soil to Silicon: The Rise of Agriculture AI and Drone Innovations in 2025
-

 Sports4 weeks ago
Sports4 weeks agoFIVB Men’s Volleyball Nations League 2025: Full Schedule, Fixtures, Format, Teams, Pools and How to Watch
-

 Startup3 weeks ago
Startup3 weeks agoHow Instagram Is Driving Global Social Media Marketing Trends
-

 Sports3 weeks ago
Sports3 weeks agoWorld Judo Championships 2025: Full Schedule, Date, Time, Key Athletes and How to Watch
-

 Sports2 weeks ago
Sports2 weeks agoFIBA 3×3 World Cup 2025: Full Schedule, Preview, and How to Watch