Tech
Cybersecurity Management Dubai – Key Components in Building a Robust Framework

It is good that you are planning to get professional help for building a robust Cybersecurity Management Dubai. You should be aware of the key components of this framework.
A comprehensive approach to cybersecurity is important these days. Even, it is important to take some actions against increasing cyber threats proactively to safeguard your business. Thankfully, experts in cybersecurity management Dubai can help you ease this process. Indeed, you have planned to get professional help to develop a cybersecurity management framework for your business. However, it would be good if you knew about the key components of creating a robust framework for cybersecurity.
Regular Security Audits and Assessments
You might be aware of the importance of regular cyber risk assessment. It will help with improving incident response preparedness for your business. Also, it will help with safeguarding your sensitive data. It will help you meet compliance requirements. So, when developing a cybersecurity management framework, ensure that it encompasses plans for regular security assessments and audits.
To Plan Incidence Response
You might have plans to take preventive measures. Nevertheless, incidents might happen. So, an effective cybersecurity management framework should include a well-defined incident response plan. In this plan, there should be a clear outline of the steps to be followed as soon as a security incident is spotted. In turn, damages can be minimized and coordinated and quick response becomes possible.
Employee Awareness and Training
Human errors remain a considerable factor in cybersecurity incidents. So, regular awareness programs and employee training programs are important. They will give the knowledge to your staff to spot phishing attempts. Also, they will be taught how to follow secure password practices. All in all, they will gain knowledge of their role in maintaining a secure digital atmosphere.
Threat Detection and Continuous Monitoring
A well-planned cybersecurity framework needs ongoing monitoring of networks and systems. With professional cybersecurity management, you can expect the implementation of advanced threat detection tools. With these tools, your business can spot and respond to probable security incidents. Above all, this can be done in real-time, thereby bringing down the dwell time of attackers within your network.
Access Control and Authentication
You would be interested in preventing unauthorized access to sensitive business information by unknown people. To achieve this, your cybersecurity management service should use multi-factor authentication. Also, regular review of user access can help minimize the risk of external and internal threats.
A robust cyber security management should include secured procedures and policies, risk assessment and management.
-

 Real Estate4 weeks ago
Real Estate4 weeks agoLicensed Authority in Cross-Border Transactions: How a State-Accredited Broker in Mexico Structured a U.S. IRA Purchase Abroad
-
 Tech4 weeks ago
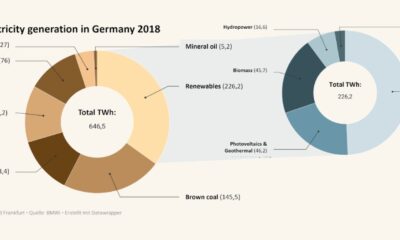
Tech4 weeks agoEnergie Quantus GmbH Highlights a Strategic Approach to Enterprise Energy and Sustainability Solutions
-

 Education4 weeks ago
Education4 weeks agoInside the World Schools Summit: The Insights Deveren Fogle Believes Every School Leader Must Understand
-

 Apps4 weeks ago
Apps4 weeks agoDigital Fairways Answers the Question: ‘What Makes Golf Course Advertising So Effective?’
-

 Lifestyle4 weeks ago
Lifestyle4 weeks agoJames Warring on Why There Are Two Sides to Every Story — And the Truth Is Usually Somewhere in Between
-

 World4 weeks ago
World4 weeks agoRev. David Jang’s Role in Advancing Youth Ministry and Education
-

 Startup3 weeks ago
Startup3 weeks agoKevin Kajy: Building Accountability Into a Growing Organization
-
 Real Estate4 weeks ago
Real Estate4 weeks agoSmart Ways To Keep Your Home Organized And Well-Maintained